-
This seems like an commercial for AMD Epyc processors till you get to that vivid yellow “answers to be had nowadays” field and understand we are speaking about Intel.
-
Intel is a founding member of the Confidential Computing Consortium, an open supply group.
Intel Company
-
Intel TSC—these days handiest appropriate to Intel (now not third-party) server motherboards—gives a list of each element gift at the board and the place it got here from.
Intel Company
-
Confidential knowledge is safe at-rest by the use of garage encryption and in-flight between programs by the use of community encryption similar to HTTPS/TLS. It might and must even be safe from rogue programs or formula directors, by the use of reminiscence encryption.
Intel Company
-
Banks are the usage of Intel SGX enclaves on Azure to permit for multi-party research of confidential knowledge.
Intel Company
At Intel’s Safety Day tournament on Tuesday, the corporate laid down its gift and destiny imaginative and prescient for security-focused options in its .
Intel’s Anil Rao and Scott Woodgate opened their presentation with a present-and-future dialogue of Intel’s SGX (Tool Guard Extensions), however their protection of the corporate’s plans to deliver Complete Reminiscence Encryption to destiny Intel CPUs was once extra attention-grabbing.
Tool Guard Extensions
Intel SGX—introduced in 2014, and introduced with the Skylake microarchitecture in 2015—is among the first encryption applied sciences designed to offer protection to spaces of reminiscence from unauthorized customers, as much as and together with the formula directors themselves. SGX is a suite of x86_64 CPU directions which permits a procedure to create an “enclave” inside reminiscence which is encrypted. Knowledge saved within the encrypted enclave is handiest decrypted throughout the CPU—or even then, it is just decrypted on the request of directions achieved from throughout the enclave itself.
Consequently, even anyone with root (formula administrator) get admission to to the working formula can not usefully learn or regulate SGX-protected enclaves. That is supposed to permit confidential, high-stakes knowledge processing to be safely conceivable on shared programs—similar to cloud VM hosts. Enabling this sort of workload to transport out of in the neighborhood owned-and-operated knowledge facilities and into massive-scale public clouds permits for more economical operation in addition to probably higher uptime, scalability, or even decrease energy intake.
Intel’s SGX has a number of issues. The primary and most evident is that it’s proprietary and vendor-specific—when you design an utility to make use of SGX to offer protection to its reminiscence, that utility will handiest run on Intel processors. The second one is that you simply should design your utility round SGX—you’ll be able to’t simply turn a transfer and switch it on.
SGX enclaves also are restricted in measurement. All enclaves on a formula should are compatible into the Enclave Web page Cache, which is these days restricted to 128MiB overall—now not 128MiB in line with procedure. Clearly, you’ll be able to’t are compatible total running programs—and even maximum bins—in handiest 128MiB, this means that that utility builders should make cautious and very tricky selections about which portions of reminiscence are “confidential” and which aren’t.
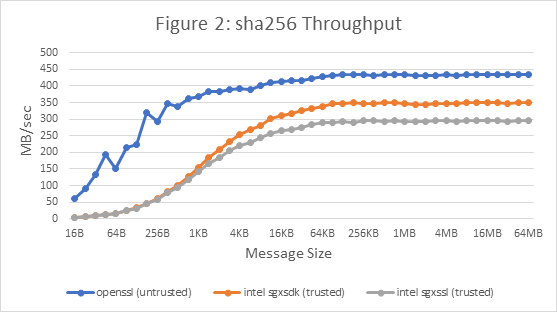
IBM’s Danny Harnik examined a number of purposes inside of SGX enclaves, together with sgx_sha256_msg, equipped through the Intel sgxsdk API.
In the end, there are probably serious efficiency affects to usage of SGX. IBM’s Danny Harnik examined SGX efficiency moderately widely in 2017, and he discovered that many commonplace workloads may simply see a throughput lower of 20 to 50 % when achieved inside of SGX enclaves.
Harnik’s checking out wasn’t 100 % absolute best, as he himself made transparent—specifically, in some instances his compiler perceived to produce less-optimized code with SGX than it had with out. Even supposing one makes a decision to handwave the ones instances as “almost definitely fixable,” they serve to spotlight an previous criticism—the want to sparsely broaden programs particularly for SGX use instances, now not simply turn a hypothetical “sure, encrypt this please” transfer.
Complete Reminiscence Encryption
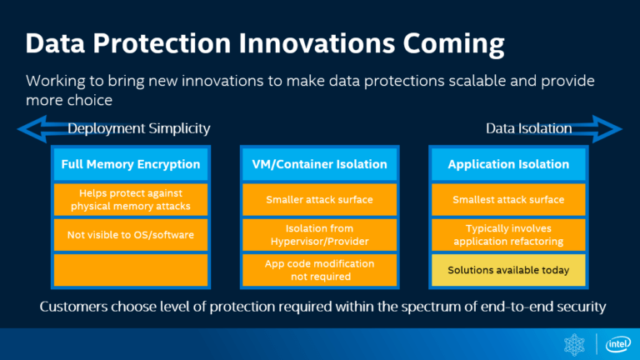
For the instant, Tool Guard Extensions are the one Intel providing to be had. However after discussing real-world use of SGX, Rao moved directly to destiny Intel applied sciences—particularly, full-memory encryption. Intel refers to its model of full-memory encryption as TME (Overall Reminiscence Encryption) or MKTME (Multi-Key Overall Reminiscence Encryption). Sadly, the ones options are vaporware for the instant. Even if Intel submitted a huge Linux kernel patchset closing Would possibly for enabling the ones options, there are nonetheless no real-world processors that supply them.
With out a TME or MKTME enabled processors to be had, it is smart to provide an explanation for the fundamental technological ideas the usage of the identical applied sciences that do exist nowadays—AMD’s SME (Protected Reminiscence Encryption) and SEV (Protected Encrypted Virtualization). For obtrusive causes, this wasn’t part of Intel’s presentation—however it is the handiest means to discuss the ideas in an already-implemented, real-world sense.
In 2016, AMD proposed a brand new generation to safe reminiscence from unauthorized customers, known as SME (Protected Reminiscence Encryption). Not like Intel’s SGX, SME would permit any web page in RAM to be encrypted and decrypted in . Any web page marked for encryption could be encrypted with an ephemeral 128-bit AES key—generated by the use of RNG (random quantity generator) at each and every reboot. Those ephemeral keys are handiest out there to the CPU itself and can’t be uncovered to customers (together with root or formula administrator stage customers).
SME, like SGX, calls for some making plans at the a part of builders. On the other hand, a stricter subset of SME, known as TSME—Clear Protected Reminiscence Encryption—would permit for the whole thing of formula RAM to be encrypted the usage of SME. As an entire-system characteristic, TSME is enabled or disabled in formula BIOS (or UEFI), and it calls for no particular making plans at the a part of utility builders—as soon as enabled, the entirety’s encrypted, and that is the reason all there’s to mention about it.
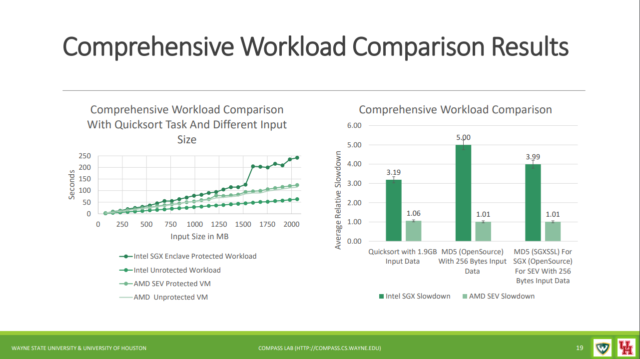
AMD’s solution to reminiscence encryption additionally comes to a long way much less efficiency have an effect on than Intel SGX. In a 2018 presentation, researchers from Wayne State College and the College of Houston confirmed maximum workloads completely unimpacted through Protected Encryption Virtualization (a subset of AMD’s SME that permits whole-VM encryption, with a separate key used for each and every lined digital gadget), in spite of vital efficiency affects with Intel’s SGX.
Since Intel’s TME and MKTME are—for the instant—nonetheless hypothetical, it is too quickly to make any daring predictions about what their efficiency have an effect on can be. However with AMD’s instance in entrance folks, it sort of feels affordable to be expecting they must have little genuine efficiency have an effect on in use, in contrast to SGX.
Conclusions
That is almost definitely a hard time to offer thrilling displays on Intel’s safety roadmap. Speculative prediction vulnerabilities have harm Intel’s processors significantly greater than their competition’, and the corporate has been crushed considerably to marketplace through sooner, easier-to-use reminiscence encryption applied sciences as smartly.
Rao and Woodgate put a courageous face on issues through speaking up how SGX has been and is being utilized in Azure. However it sort of feels obvious that the systemwide solution to reminiscence encryption already applied in AMD’s Epyc CPUs—or even in a few of their desktop line—may have a a long way higher lasting have an effect on. Intel’s slides about their very own upcoming complete reminiscence encryption are classified “inventions,” however they appear much more like catching as much as their already-established festival.
Record symbol through Intel Company



