
Nonetheless smarting from closing month’s sell off of telephone numbers belonging to 500 million Fb customers, the social media large has a brand new privateness disaster to cope with: a device that, on a mass scale, hyperlinks the Fb accounts related to e mail addresses, even if customers select settings to stay them from being public.
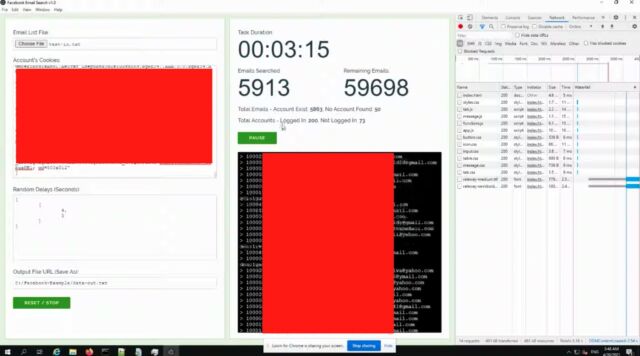
A video circulating on Tuesday confirmed a researcher demonstrating a device named Fb Electronic mail Seek v1.zero, which he stated may hyperlink Fb accounts to as many as five million e mail addresses in keeping with day. The researcher—who stated he went public after Fb stated it did not suppose the weak point he discovered used to be “vital” sufficient to be mounted—fed the software a listing of 65,000 e mail addresses and watched what took place subsequent.
“As you’ll see from the output log right here, I am getting an important quantity of effects from them,” the researcher stated because the video confirmed the software crunching the cope with listing. “I have spent possibly $10 to shop for 200-odd Fb accounts. And inside of 3 mins, I’ve controlled to do that for six,000 [email] accounts.”
Ars got the video on situation the video now not be shared. A complete audio transcript seems on the finish of this submit.
Losing the ball
In a commentary, Fb stated: “Apparently that we erroneously closed out this worm bounty file ahead of routing to the right staff. We recognize the researcher sharing the guidelines and are taking preliminary movements to mitigate this factor whilst we apply as much as higher perceive their findings.”
A Fb consultant did not reply to a query asking if the corporate instructed the researcher it did not believe the vulnerability vital sufficient to warrant a repair. The consultant stated Fb engineers imagine they have got mitigated the leak by means of disabling the method proven within the video.
The researcher, whom Ars agreed to not establish, stated that Fb Electronic mail Seek exploited a front-end vulnerability that he reported to Fb just lately however that “they [Facebook] don’t believe to be vital sufficient to be patched.” Previous this 12 months, Fb had a identical vulnerability that used to be in the long run mounted.
“That is necessarily the very same vulnerability,” the researcher says. “And for some explanation why, in spite of me demonstrating this to Fb and making them conscious about it, they have got instructed me immediately that they’re going to now not be taking motion towards it.”
On Twitter
Fb has been underneath hearth now not only for offering the approach for those huge collections of knowledge, but in addition how it actively tries to advertise the theory they pose minimum hurt to Fb customers. An e mail Fb inadvertently despatched to a reporter on the Dutch newsletter DataNews prompt public family members other people to “body this as a extensive business factor and normalize the truth that this process occurs ceaselessly.” Fb has additionally made the respect between scraping and hacks or breaches.
It is not transparent if somebody actively exploited this worm to construct an enormous database, however it indubitably would not be sudden. “I imagine this to be moderately a perilous vulnerability, and I would really like assist in getting this stopped,” the researcher stated.
This is the written transcript of the video:
So, what I want to exhibit this is an lively vulnerability inside of Fb, which permits malicious customers to question, um, e mail addresses inside of Fb and feature Fb go back, any matching customers.
Um, this works with a entrance finish vulnerability with Fb, which I have reported to them, made them conscious about, um, that they don’t believe to be vital sufficient to be patched, uh, which I’d believe to be moderately an important, uh, privateness violation and a large drawback.
This technique is recently being utilized by tool, which is to be had presently throughout the hacking neighborhood.
Lately it is getting used to compromise Fb accounts for the aim of taking up pages teams and, uh, Fb promoting accounts for clearly financial achieve. Um, I have arrange this visible instance inside of no JS.
What I have carried out this is I have taken, uh, 250 Fb accounts, newly registered Fb accounts, which I have bought on-line for approximately $10.
Um, I’ve queried or I am querying 65,000 e mail addresses. And as you’ll see from the output log right here, I am getting an important quantity of effects from them.
If I take a look on the output document, you’ll see I’ve a consumer ID title and the e-mail cope with matching the enter e mail addresses, which I’ve used. Now I’ve, as I say, I have spent possibly $10 the use of two to shop for 200-odd Fb accounts. And inside of 3 mins, I’ve controlled to do that for six,000 accounts.
I’ve examined this at a bigger scale, and it’s conceivable to make use of this to extract feasibly as much as five million e mail addresses in keeping with day.
Now there used to be an present vulnerability with Fb, uh, previous this 12 months, which used to be patched. That is necessarily the very same vulnerability. And for some explanation why, in spite of me demonstrating this to Fb and making them conscious about it, um, they have got instructed me immediately that they’re going to now not be taking motion towards it.
So I’m attaining out to other people reminiscent of yourselves, uh, in hope that you’ll use your affect or contacts to get this stopped, as a result of I’m very, very assured.
This isn’t handiest an enormous privateness breach, however this may lead to a brand new, any other huge information sell off, together with emails, which goes to permit unwanted events, now not handiest to have this, uh, e mail to consumer ID suits, however to append the e-mail cope with to telephone numbers, which were to be had in earlier breaches, um, I am moderately glad to exhibit the entrance finish vulnerability so you’ll see how this works.
I am not going to turn it on this video just because I are not looking for the video to be, um, I are not looking for the technique to be exploited, but when I’d be moderately glad to, to exhibit it, um, if this is essential, however as you’ll see, you’ll see continues to output an increasing number of and extra. I imagine this to be moderately a perilous vulnerability and I would really like assist in getting this stopped.



