As many as 1,500 companies all over the world had been inflamed via extremely harmful malware that first struck instrument maker Kaseya. In some of the worst ransom assaults ever, the malware, in flip, used that get right of entry to to fell Kaseya’s shoppers.
The assault struck on Friday afternoon within the lead-up to the three-day Independence Day vacation weekend in america. Hackers affiliated with REvil, one among ransomware’s maximum cutthroat gangs, exploited a zero-day vulnerability within the Kaseya VSA far off control carrier, which the corporate says is utilized by 35,000 shoppers. The REvil associates then used their keep watch over of Kaseya’s infrastructure to push a malicious instrument replace to shoppers, who’re basically small-to-midsize companies.
Endured escalation
In a observation posted on Monday, Kaseya stated that more or less 50 of its shoppers have been compromised. From there, the corporate stated, 800 to at least one,500 companies which are controlled via Kaseya’s shoppers have been inflamed. REvil’s website online at the darkish internet claimed that greater than 1 million goals have been inflamed within the assault and that the crowd used to be not easy $70 million for a common decryptor.
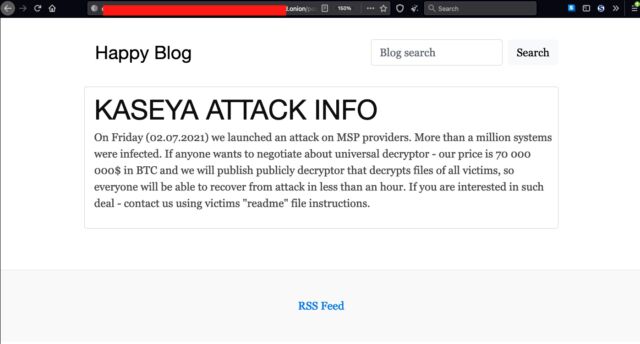
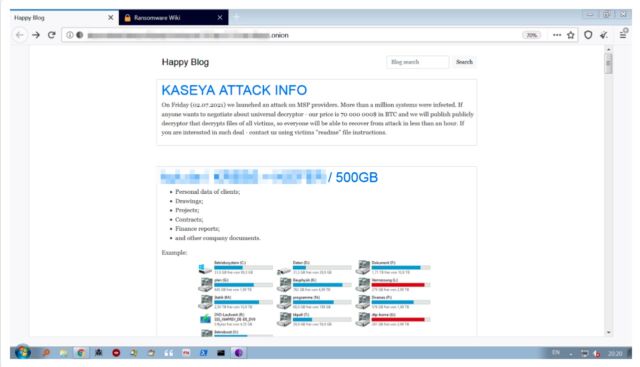
REvil’s website online were up to date to take away a picture purportedly appearing arduous drives with 500GB of knowledge locked up. Ransomware teams continuously take away data from their websites as soon as ransom negotiations start as an indication of excellent religion. Right here’s how the picture seemed prior to now:
Cybereason
“It’s not a perfect signal that a ransomware gang has a 0 day in a product used broadly via Controlled Carrier Suppliers, and displays the continuing escalation of ransomware gangs—which I’ve written about earlier than,” safety professional and unbiased researcher Kevin Beaumont wrote.
The mass assault had cascading results all over the world. Swedish grocery store chain Coop on Tuesday used to be nonetheless seeking to get better after it close about part of its 800 shops as a result of point-of-sale tills and self-service checkouts stopped running. Colleges and kindergartens in New Zealand have been additionally affected, as have been some public management places of work in Romania. Germany’s cybersecurity watchdog, BSI, stated on Tuesday that it used to be conscious about 3 IT carrier suppliers in Germany which were affected. The map underneath displays the place safety company Kaspersky is seeing infections.
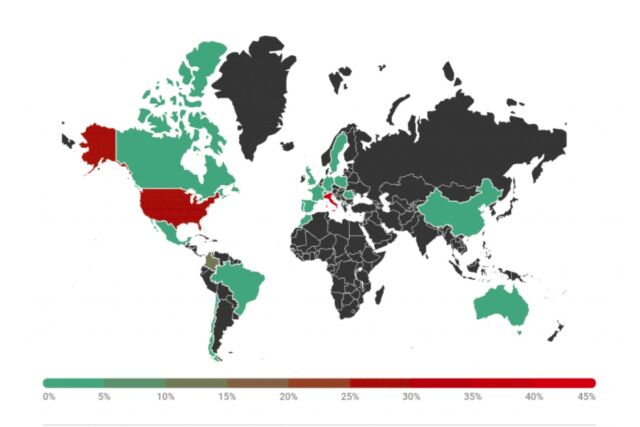
Kaspersky
REvil has earned a name as a ruthless and complex team, even in notoriously brazen ransomware circles. Its most up-to-date big-game sufferer used to be meatpacking large JBS, which in June close down an enormous swath of its global operations after the ransomware hamstrung its computerized processes. JBS in the end paid REvil associates $11 million.
REvil’s earlier sufferers come with Taiwanese multinational electronics company Acer in March in addition to try in April to extort Apple following an assault towards one among its industry companions. REvil may be the crowd that hacked Grubman Shire Meiselas & Sacks, the fame legislation company that represented Woman Gaga, Madonna, U2, and different top-flight entertainers. When REvil demanded $21 million in go back for no longer publishing the information, the legislation company reportedly presented $365,000. REvil replied via upping its call for to $42 million and later publishing a 2.4GB archive containing some Woman Gaga prison paperwork.
Nonetheless different REvil sufferers come with Kenneth Copeland, SoftwareOne, Quest, and Travelex.
Surgical precision
This weekend’s assault used to be performed with nearly surgical precision. Consistent with Cybereason, the REvil associates first received get right of entry to to focused environments after which used the zero-day within the Kaseya Agent Track to realize administrative keep watch over over the objective’s community. After writing a base-64-encoded payload to a report named agent.crt the dropper completed it.
Right here’s the glide of the assault:
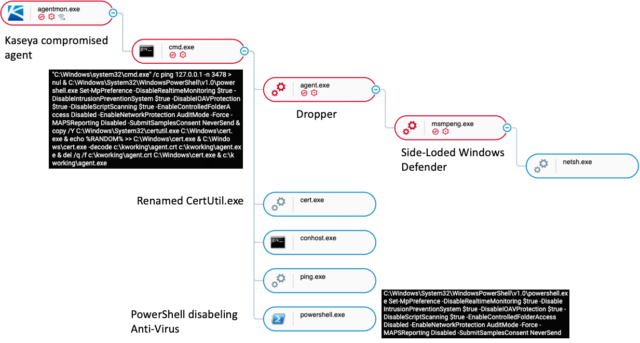
Cybereason
The ransomware dropper Agent.exe is signed with a Home windows-trusted certificates that makes use of the registrant identify “PB03 TRANSPORT LTD.” Via digitally signing their malware, attackers are ready to suppress many safety warnings that might differently seem when it’s being put in. Cybereason stated that the certificates seems to had been used solely via REvil malware that used to be deployed all over this assault.
So as to add stealth, the attackers used a method referred to as DLL Facet-Loading, which puts a spoofed malicious DLL report in a Home windows’ WinSxS listing in order that the working gadget so much the spoof as a substitute of the respectable report. Within the case right here, Agent.exe drops an old-fashioned model this is susceptible to DLL Facet-Loading of “msmpeng.exe,” which is the report for the Home windows Defender executable.
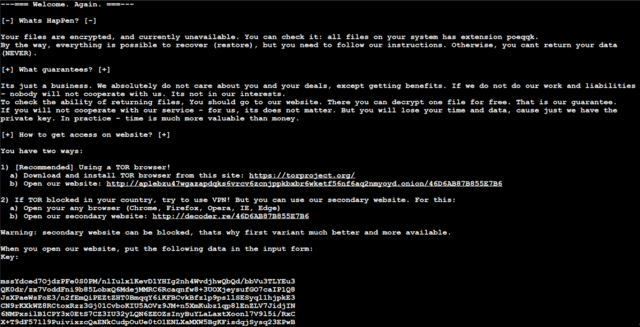
As soon as completed, the malware adjustments the firewall settings to permit native home windows techniques to be came upon. Then, it begins to encrypt the information at the gadget and presentations the next ransom notice:
Cybereason
The development is the newest instance of a delivery chain assault, during which hackers infect the supplier of a broadly used services or products with the objective of compromising downstream shoppers who use it. On this case, the hackers inflamed Kaseya shoppers after which used that get right of entry to to contaminate the companies that won carrier from Kaseya.
The SolarWinds compromise came upon in December used to be every other such supply-chain assault. It used SolarWinds hacked instrument construct infrastructure to push a malicious instrument replace to 18,000 organizations that used the corporate’s community control software. About 9 federal businesses and 100 non-public organizations won follow-on infections.
Any individual who suspects their community has been affected whatsoever on this assault must examine instantly. Kaseya has printed a software that VSA shoppers can use to stumble on infections of their networks. The FBI and the Cybersecurity and Infrastructure Safety Company have collectively issued suggestions for Kaseya shoppers, specifically in the event that they’ve been compromised.



