
SAN FRANCISCO—Malware builders are at all times seeking to outdo each and every different with creations which can be stealthier and extra complicated than their competition’. On the RSA Safety convention this week, a former hacker for the Nationwide Safety Company demonstrated an means that’s steadily more practical: stealing after which repurposing a rival’s code.
Patrick Wardle, who’s now a safety researcher on the macOS and iOS endeavor control company Jamf, confirmed how reusing previous Mac malware could be a smarter and no more resource-intensive means for deploying ransomware, faraway get admission to undercover agent gear, and different sorts of malicious code. The place the means in point of fact can pay dividends, he mentioned, is with the repurposing of complicated code written through government-sponsored hackers.
“There are extremely well-funded, well-resourced, very motivated hacker teams in three-letter businesses which can be developing wonderful malware that’s totally featured and in addition totally examined,” Wardle mentioned all through a chat titled “Repurposed Malware: A Darkish Facet of Recycling.”
“The speculation is: why no longer let those teams in those businesses create malware and when you’re a hacker simply repurpose it on your personal undertaking?” he mentioned.
Hijacking the hijackers
To end up the purpose, Wardle described how he altered 4 items of Mac malware which were utilized in in-the-wild assaults over the last a number of years.
The repurposing led to the malware to report back to command servers belonging to Wardle somewhat than the servers designated through the builders. From there, Wardle had complete keep an eye on over the recycled malware. The feat allowed him to make use of well-developed and completely featured packages to put in his personal malicious payloads, download screenshots and different delicate knowledge from compromised Macs, and perform different nefarious movements written into the malware.
But even so saving time and sources, malware repurposing supplies two key advantages:
- It’ll permit attackers, in particular the ones from state-sponsored teams, to contaminate high-risk environments, akin to the ones which can be already inflamed and beneath the attention of alternative malicious device actors. In that place, many country state hacking teams will forgo deploying their crown-jewel malware to stay proprietary techniques, ways, and procedures non-public. Repurposing any person else’s malware may well be an acceptable choice in those situations.
- Within the tournament that the malware an infection is detected and forensically analyzed, there is a just right probability that researchers will misattribute the assault to the unique hackers and no longer the birthday celebration that repurposed the malware
There’s no scarcity of proof that the repurposing of opponents’ malware is already a commonplace apply amongst countryside hackers. WannaCry and NotPetya—the worms that wreaked international pc shutdowns in 2017 and are broadly attributed to North Korea and the Russian Federation respectively—unfold hastily from pc to pc with the most important lend a hand from EternalBlue, the Home windows exploit evolved through, and later stolen from, the Nationwide Safety Company. Researchers at safety company Symantec discovered a hacking workforce broadly tied to the Chinese language authorities reused NSA malware that will get put in through EternalBlue, in March 2016, 14 months prior earlier than the tough NSA hacking gear have been printed. This 2017 article through freelance reporter Kim Zetter stories that recordsdata printed through Wikileaks confirmed CIA hackers recycling ways and snippets of code utilized in earlier assaults to be used in new tasks. A couple of years in the past, consistent with proof unearthed through Symantec, the Russian-speaking hacker workforce referred to as Turla hijacked the servers of OilRig, a rival outfit hooked up to Iran’s authorities. Turla then used the infrastructure to assault a Center Japanese authorities.
Getting Jeused
Considered one of Wardle’s repurposings concerned AppleJeus.c, a work of just lately found out malicious code embedded in a faux cryptocurrency buying and selling app for macOS. The pattern was once notable for being the primary, or no less than some of the first, identified malware specimens for macOS to make use of an in-memory, or fileless, solution to execute second-stage malicious payloads onto focused Macs.
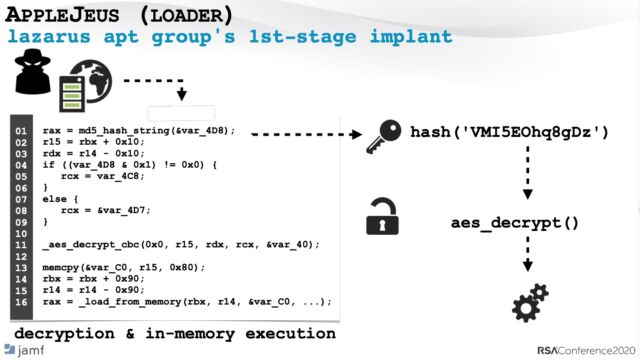
By means of executing malicious code only in reminiscence—somewhat than the usage of the extra commonplace course of saving the code to disk after which executing it—AppleJeus.c considerably reduced the possibilities antivirus systems and different kinds of endpoint safety would stumble on the an infection or be capable to seize the second-stage payloads. Researchers have tied the malware to Lazarus, a hacker workforce running for the North Korean authorities.
Quite than increase his personal fileless payload installer for macOS, Wardle made only one minor amendment to AppleJeus.c: as an alternative of acquiring the fileless payload from the server at the start hardcoded into AppleJeus.c, the changed malware now were given the payload from a server he managed.
“Which means when the [first stage of the] malware is performed, it is going to now communicate to our server as an alternative of the hacker’s authentic infrastructure, and it is going to create the customized command and keep an eye on server that programs off the payload,” Wardle mentioned.
Step one was once to completely analyze the interior workings of AppleJeus.c. Some of the issues he noticed have been the malware’s functions and the protocol it used to be in contact with the unique builders’ command and keep an eye on server. The use of a disassembler, as an example, he noticed the malware the usage of a cryptographic hashing serve as and a decryption serve as to load after which execute the second-stage payload.
By means of the usage of a debugger to prevent the malware simply earlier than it ran the hashing serve as, he discovered the string VMI5EOhq8gDz, which when handed to the hash serve as became out to be the decrpytion key. He then used the disassembler and debugger to find the decryption cipher and parameters similarly.
Subsequent, Wardle used a hex editor to modify the unique model’s hard-coded keep an eye on server area to the cope with of the server beneath his keep an eye on. He designed this new keep an eye on server to make use of the similar conversation protocol and to engage step-by-step with each and every serve as of the malware.
To get the changed model of AppleJeus.c to simply accept the second-stage payload, Wardle’s keep an eye on server needed to, amongst different issues, encrypt it with the similar key and cipher he noticed all through his research. With that, Wardle may just use his repurposed AppleJeus.c to load and execute any Mac mach-O executable report of his selection.
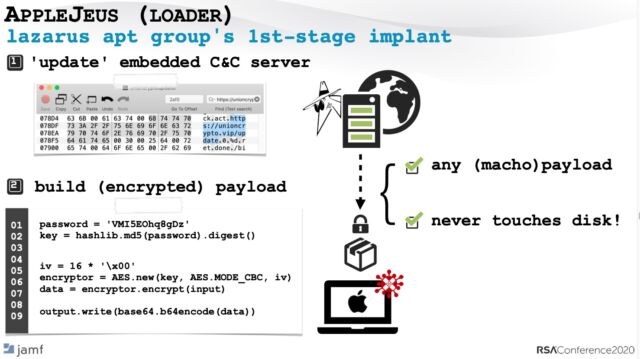
“With a unmarried amendment to the binary, (and construction a lightweight C&C server), we’ve got get admission to to a sophisticated countryside loader that can carry out to our bidding …with no need to put in writing any (client-side) code!” Wardle wrote in a message following his communicate. “That is means more straightforward than writing it from scratch 🙂 Additionally, if this repurposed variant is ever detected, it is going to most probably be misattributed again to the North Koreans.”
As a fascinating apart, a lot of the code used to hold out AppleJeus.c’s in-memory an infection was once itself lifted from a deep-dive technical research printed through Cylance researcher Stephanie Archibald.
3 times extra with feeling
Wardle used an identical ways to repurpose 3 different items of Mac malware that experience circulated within the wild. The malware incorporated Fruitfly, a faraway get admission to device that stole tens of millions of consumer pictures, a lot of them nudes, over 13 years earlier than after all being shutdown, a ransomware app found out in 2016, and Windtail, which focused most commonly authorities businesses and corporations within the Center East.
Wardle was once in a position to make different tweaks to his repurposed items of code so they’d bypass malware mitigations inbuilt to macOS. As an example, for the reason that Xprotect malware scanner is according to report signatures, converting a unmarried byte of reused code is enough for it to fully get away detection. And when Apple-issued signing certificate had been revoked, it’s trivial to unsign the device and signal it with a brand new certificates. And to take away warnings displayed when customers attempt to execute code or set up apps downloaded from the Web, it’s simple to take away the programming flags that make the ones warnings seem.
This week’s RSA communicate can give the influence that malware repurposing is exclusive to Mac choices. The examples of recycled malicious code discussed previous will have to shed light on that this type of recycling works in opposition to any working machine or platform. Given the wealth of running malware and the benefit in reusing it, it’s simple to know why the apply is so commonplace, Wardle mentioned. “The speculation is to let the ones with extra time, cash, and sources do the entire difficult paintings.”



